Online event security is a hot topic at the moment and this is an area where Zoom are going the extra mile to give you peace of mind. Ten years ago, Zoom set out to become the best video-first communications platform. Today they’ve exceeded 200 million users worldwide and counting. With over 10 million meetings taking place each day between schools, universities, governments, companies and corporations, keeping users safe within the confines of the platform is the priority of all practices.
As well as all the work that goes on behind the scenes, keeping users informed and up to date on security features and issues is paramount to the ongoing protection of everyone’s data and privacy. In addition to using many of the security pre-sets Zoom has automated within the platform, by following a few simple checks you can keep your cloud-based business contributions under lock and key.
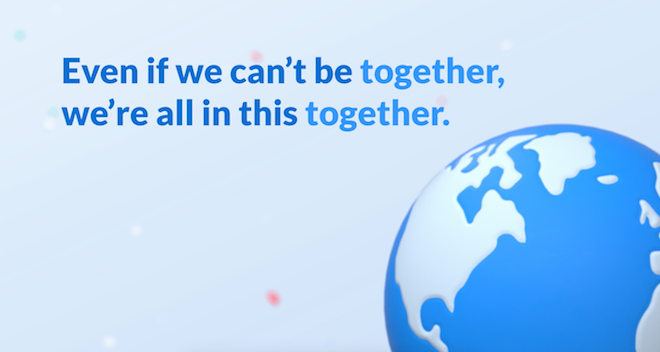
You’ll want to familiarise yourself with all the security and privacy settings. Most settings can be set to default through your web settings on the dashboard. In light of the massive influx of new users Zoom has experienced over the last few months, they’ve locked down the settings as a standard, leaving you to unlock as you deem fit. However, if you are posting a public event, to a public forum such as Facebook, remember that once the information is out there it’s accessible by anyone.
With a public event you can generate a random meeting ID. If you use that ID for your public event, once the event has finished you’re a lot less likely to receive any unwanted traffic to your personal meeting ID (PMI). Your PMI acts like a phone number would. It is personalised to you and you’re contactable through it at any point.
Something else you may want to address on a public event is screen control. You want to keep the control of the screen to yourself to save anyone interfering and you can restrict access before or even during the event. Before the event make sure you head to the host control bar and the share screen option to ‘one participant can share at a time’. During an event using the host controls at the bottom, click through – share screen – advanced sharing options – who can share? and choose ‘only host’.
What About User Control?
Another great feature for helping you set up a public event is ‘the waiting room’. This virtual waiting area is a great tool when it comes to organising your participants. You can leave a message for guests waiting so they know they’re in the right place. You can use this message to reiterate any rules or guidelines for your events that viewers need to be aware of. The waiting room comes in handy for screening who’s present in your event and drop any unwanted attention before the event has started.
Outside of the waiting room and into the action, you can live manage your viewers during the event. You can choose to remove viewers permanently during an event by simply hovering over their profile and selecting it from the options. Through the online event security settings you can decide whether to allow ‘kicked’ users to log back in or not.
https://youtube.com/watch?v=p1IMmOujc9c
What Other Security Features Does Zoom Have?
A great feature for public events is only allowing registered users entry to the event. This means that if a viewer is just browsing Zoom as a guest, they would be denied permission to the event.
Other noteworthy features linked to the handling of your viewers are; setting up your own two-factor authentication. With this function you can publish the live event anywhere you feel, but only supply the password to your chosen crowd; lock the meeting enables you to lock out a meeting or event stopping any new viewers joining; Place on hold feature allows you to place individual users or all users on hold at any point; disable video turns off the video of viewers, at the hosts discretion; turn off annotation puts you in charge of who is annotating the screen share.
There are of course many more features throughout the platform that enable you to keep a tight grip on the security and privacy of your event. They not only help with tailoring the event to your own needs but give you options to help iron out any issues that may arise. People across the globe use Zoom for many different reasons, so accessible and manageable functionality puts the ball in your court whilst maintaining a respectable amount of responsibility on Zooms behalf.

Understanding a platforms capability plays a large part in benefitting from its maximum potential. Aside from all the fantastic work the Zoom team put into their platform’s inbuilt tutorials, the internet is currently littered with blogs and courses teaching you to the best way to manage your conference software, many will use Zoom. With an extra bit of tuition, you can make your light show a firework display. For any issues that may pop up, the help and support section of the interface is always accessible and will guide you through frequently asked questions and answers to keep things running smoothly. Online Event Security is at the heart of Zoom’s ethos and you can always reach out to support if you ever feel the need to.
Due to the huge rise in schools, universities and governments now reliant on the app for much of their day to day interaction, security must remain at the core of Zooms ethos. The teamwork tirelessly on feedback from users with the sole intent of creating a safer environment.
Zoom 5.0 marks a key milestone in their 90-day plan which entails the identification, address and upgrade of Zooms security and privacy functions. With additional support for 256-bit GCM encryption, moving forward Zoom will be providing further data and tampering protection. Eric Yuan, CEO said “I am proud to reach this step in our 90-day plan, but this is just the beginning. We built our business by delivering happiness to our customers. We will earn our customers’ trust and deliver them happiness with our unwavering focus on providing the most secure platform.”
We are the official Zoom Integration Partner in the Middle East. Click here to speak to our sales team about how we can integrate Zoom 5.0 into your business!